Some highlights of Microsoft’s “Internet-Based Services Agreement” for MSDN Subscriptions
Posted: 18 August 2016 Filed under: Uncategorized Leave a commentSo, it turns out that this portion is about Windows Server 2012 R2. Kind of noisy. If you don’t want this information sent, or these actions taken, without your consent, you should switch some of it off.
INTERNET-BASED SERVICES. Microsoft provides Internet-based services with the software. It may change or cancel them at any time.
- Consent for Internet-Based Services. The software features described below and in the Windows Server Privacy Highlights connect to Microsoft or service provider computer systems over the Internet. In some cases, you will not receive a separate notice when they connect. You may switch off these features or not use them. For more information about these features, go to go.microsoft.com/fwlink/?linkid=280262. By using these features, you consent to the transmission of this information. Microsoft does not use the information to identify or contact you.Computer Information. The following features use Internet protocols, which send to the appropriate systems computer information, such as your Internet protocol address, the type of operating system, browser and name and version of the software you are using, and the language code of the device where you run the software. Microsoft uses this information to make the Internet-based services available to you.
- Windows Update Feature. You may connect new hardware to the device where you run the software. Your device may not have the drivers needed to communicate with that hardware. If so, the update feature of the software can obtain the correct driver from Microsoft and run it on your device. You can switch off this update feature.
- Web Content Features. Features in the software can retrieve related content from Microsoft and provide it to you. To provide the content, these features send to Microsoft the type of operating system, name and version of the software you are using, type of browser and language code of the device where you run the software. Examples of these features are clip art, templates, online training, online assistance and Appshelp. You may choose not to use these web content features.
- Digital Certificates. The software uses digital certificates. These digital certificates confirm the identity of Internet users sending X.509 standard encrypted information. They also can be used to digitally sign files and macros, to verify the integrity and origin of the file contents. The software retrieves certificates and updates certificate revocation lists. These security features operate only when you use the Internet.
- Auto Root Update. The Auto Root Update feature updates the list of trusted certificate authorities. You can switch off the Auto Root Update feature.
- Windows Media Digital Rights Management. Content owners use Windows Media digital rights management technology (WMDRM) to protect their intellectual property, including copyrights. This software and third party software use WMDRM to play and copy WMDRM-protected content. If the software fails to protect the content, content owners may ask Microsoft to revoke the software’s ability to use WMDRM to play or copy protected content. Revocation does not affect other content. When you download licenses for protected content, you agree that Microsoft may include a revocation list with the licenses. Content owners may require you to upgrade WMDRM to access their content. Microsoft software that includes WMDRM will ask for your consent prior to the upgrade. If you decline an upgrade, you will not be able to access content that requires the upgrade. You may switch off WMDRM features that access the Internet. When these features are off, you can still play content for which you have a valid license.
- Windows Media Player. When you use Windows Media Player, it checks with Microsoft for
- compatible online music services in your region;
- new versions of the player; and
- codecs if your device does not have the correct ones for playing content.You can switch off this last feature. For more information, go to www.microsoft.com/windows/windowsmedia/player/12/privacy.aspx.
- Malicious Software Removal. During setup, if you select “Get important updates for installation”, the software may check and remove certain malware from your device. “Malware” is malicious software. If the software runs, it will remove the Malware listed and updated atwww.support.microsoft.com/?kbid=890830. During a Malware check, a report will be sent to Microsoft with specific information about Malware detected, errors, and other information about your device. This information is used to improve the software and other Microsoft products and services. No information included in these reports will be used to identify or contact you. You may disable the software’s reporting functionality by following the instructions found at www.support.microsoft.com/?kbid=890830. For more information, read the Windows Malicious Software Removal Tool privacy statement at go.microsoft.com/fwlink/?LinkId=113995.
- Network Awareness. This feature determines whether a system is connected to a network by either passive monitoring of network traffic or active DNS or HTTP queries. The query only transfers standard TCP/IP or DNS information for routing purposes. You can switch off the active query feature through a registry setting.
- Windows Time Service. This service synchronizes with time.windows.com once a week to provide your computer with the correct time. You can turn this feature off or choose your preferred time source within the Date and Time Control Panel applet. The connection uses standard NTP protocol.
- IPv6 Network Address Translation (NAT) Traversal service (Teredo). This feature helps existing home Internet gateway devices transition to IPv6. IPv6 is a next generation Internet protocol. It helps enable end-to-end connectivity often needed by peer-to-peer applications. To do so, each time you start up the software the Teredo client service will attempt to locate a public Teredo Internet service. It does so by sending a query over the Internet. This query only transfers standard Domain Name Service information to determine if your computer is connected to the Internet and can locate a public Teredo service. If you
- use an application that needs IPv6 connectivity or
- configure your firewall to always enable IPv6 connectivity
- by default standard Internet Protocol information will be sent to the Teredo service at Microsoft at regular intervals. No other information is sent to Microsoft. You can change this default to use non-Microsoft servers. You can also switch off this feature using a command line utility named “netsh”.
- Windows Server 2012 Active Directory Rights Management Services. The software contains a feature that allows you to create content that cannot be printed, copied or sent to others without your permission. For more information, go to www.microsoft.com/rms. You may choose not to use this feature.
- Accelerators. When you use click on or move your mouse over an Accelerator, the title and full web address or URL of the current webpage, as well as standard computer information, and any content you have selected, might be sent to the service provider. If you use an Accelerator provided by Microsoft, the information sent is subject to the Microsoft Online Privacy Statement, which is available at go.microsoft.com/fwlink/?linkid=31493. If you use an Accelerator provided by a third party, use of the information sent will be subject to the third party’s privacy practices.
- Use of Information. Microsoft may use the computer information, Accelerator information, and Malware reports to improve our software and services. We may also share it with others, such as hardware and software vendors. They may use the information to improve how their products run with Microsoft software.
- Misuse of Internet-based Services. You may not use these services in any way that could harm them or impair anyone else’s use of them. You may not use the services to try to gain unauthorized access to any service, data, account or network by any means.
Neural networks for automobiles
Posted: 28 June 2016 Filed under: security, Uncategorized | Tags: machine learning Leave a commentSo… when will our cars make a real-time calculation of our likelihood of a poor decision, leading to a collision, based on our current level of distractability or our agitation? Then they could communicate to all the neighboring cars something like “give this car a wider berth” and/or apply increasingly stringent restrictions on that driver, such as maximum speed. Or take over driving entirely.
Not that I’m looking forward to it — it just seems like a natural evolution of our automobiles’ neural net.
Security in Scientific Research
Posted: 23 March 2016 Filed under: Uncategorized Leave a commentTaking a gander at this article on Science Node, something caught my eye.
A lot of the same concerns that apply in the private or corporate sector apply to us as well. Where it gets interesting for us is the standard security mantra of turn on the updates, run security software or antivirus software doesn’t work very well for us.
Automatically updated software can break the data-taking process, and anything that would take all of or part of the detector off-line can be a serious problem for us.
I acknowledge that integrity and availability are primary concerns in their environment, confidentiality less so. But in the real world, things change, and new vulnerabilities are found all the time. You can’t gain the benefits of software or firmware, without the responsibilities: providing an upgrade path.
Displaying all your tab characters in Vim
Posted: 6 October 2015 Filed under: productivity | Tags: vim Leave a commentI usually use :set expandtab in Vim, but a particular file I was editing required explicit tab characters. So I set :noexpandtab, but then realized I couldn’t tell which were tabs, and which were spaces. Easy fix:
:set list
:set listchars=tab:\|\<Space>
…where <Space> is a literal space. Thanks again to the Vim Wiki!
Comodo Free S/MIME Certificates: Too Restrictive for Prime Time?
Posted: 11 December 2014 Filed under: Uncategorized Leave a commentI was considering a free S/MIME certificate from Comodo InstantSSL, but their Subscriber Agreement reads, in part:
3.4 The Subscriber shall not use the Email Certificate to transmit (either by sending by email or uploading using any format of communications protocol), receive (either by soliciting an e-mail or downloading using any format of communications protocol), view or in any other way use any information which may be illegal, offensive, abusive, contrary to public morality, indecent, defamatory, obscene or menacing…
Which means, we’ll give you this free certificate, but you may not use it to send or receive any encrypted or signed e-mail we don’t like.
How’s that for restrictive?
No thanks.
Using BitCoin as a Public Ledger
Posted: 4 June 2013 Filed under: privacy, security | Tags: bitcoin, security 1 CommentUsing BitCoin as a Public Ledger
Interesting way to document “prior art”: create a one-way SHA256 hash of some work, then send the smallest Bitcoin amount possible to that address (use it as a wallet destination). Your hash is in the public blockchain, so you can give your document to someone else and tell them to hash it themselves, then compare to your record of the time and date.
Update: Not quite right; it’s actually a bit more more complex than that:
The document is certified via embedding its SHA256 digest in the Bitcoin blockchain. This is done by generating a valid bitcoin transaction to two specially crafted addresses which encode/contain the hash. The hash is cut in two fragments, each fragment contained in one of these addresses. The hash fragment is used as a replacement for the RIPEMD-160 hash of the public ECDSA key in the bitcoin address generation algorithm. This is why the bitcoins sent in this special transaction are unspendable, as the addresses are being generated from the document’s hash fragments instead of from a private ECDSA key.
U.S. cyber plan calls for private-sector scans of Net
Posted: 22 March 2013 Filed under: Uncategorized | Tags: privacy, security Leave a commentU.S. cyber plan calls for private-sector scans of Net
The Department of Homeland Security will gather the secret data and pass it to a small group of telecommunication companies and cybersecurity providers that have employees holding security clearances, government and industry officials said. Those companies will then offer to process email and other Internet transmissions for critical infrastructure customers that choose to participate in the program.
By using DHS as the middleman, the Obama administration hopes to bring the formidable overseas intelligence-gathering of the NSA closer to ordinary U.S. residents without triggering an outcry from privacy advocates who have long been leery of the spy agency’s eavesdropping.
Chinese Elite Hacking Unit 61398
Posted: 27 February 2013 Filed under: Uncategorized | Tags: malware, security, web application security 1 CommentChinese Elite Hacking Unit 61398
As Mandiant mapped the Internet protocol addresses and other bits of digital evidence, it all led back to the edges of Pudong district of Shanghai, right around the Unit 61398 headquarters. The group’s report, along with 3,000 addresses and other indicators that can be used to identify the source of attacks, concludes “the totality of the evidence” leads to the conclusion that “A.P.T. 1 is Unit 61398.”
Mandiant discovered that two sets of I.P. addresses used in the attacks were registered in the same neighborhood as Unit 61398’s building.
“It’s where more than 90 percent of the attacks we followed come from,” said Mr. Mandia.
The only other possibility, the report concludes with a touch of sarcasm, is that “a secret, resourced organization full of mainland Chinese speakers with direct access to Shanghai-based telecommunications infrastructure is engaged in a multiyear enterprise-scale computer espionage campaign right outside of Unit 61398’s gates.”
Drupal versus Proprietary Web Content Management Systems
Posted: 11 February 2013 Filed under: drupal, open source | Tags: drupal Leave a comment“Sloppy” mouse focus in Ubuntu Precise Pangolin 12.04
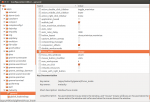
Posted: 7 December 2012 Filed under: Uncategorized | Tags: ubuntu Leave a commentHere’s how you can get your window focus to follow the mouse. Run gconf-editor, and edit “/ apps / Metacity / general / focus_mode.”